List of Meltdown and Spectre Vulnerability Advisories, Patches, & Updates
- January 3, 2018
- 09:52 PM
- 6
Two new vulnerabilities called Meltdown and Spectre, or speculative execution side-channel vulnerabilities, have been discovered in modern processors that allow malicious programs to steal information from the memory of other programs. This means that the malicious program can steal passwords, account information, encryption keys, or theoretically anything stored in the memory of a process.
Vendors have started to release information on how customers can protect themselves from Spectre or Meltdown and the status of their services. To make it easier to find this information, I will be adding links to various advisories as they are released. The related CVEs are CVE-2017-5753, CVE-2017-5715, and CVE-2017-5754.
It is important to note, though, that a software update will not be able to completely resolve these vulnerabilities. It is also important to make sure you have the latest bios/firmware updates for your laptop or computer installed as well.
For those who want to monitor these updates, I suggest you check this page throughout the coming days to see if new information is available.
For more detailed information about the Spectre and Meltdown vulnerabilities, you can read our coverage in the articles below:
- How to Check and Update Windows Systems for the Meltdown and Spectre CPU Flaws
- Mozilla Confirms Web-Based Execution Vector for Meltdown and Spectre Attacks
- Microsoft Releases Emergency Updates to Fix Meltdown and Spectre CPU Flaws
- Google: Almost All CPUs Since 1995 Vulnerable To “Meltdown” And “Spectre” Flaws
- Intel Denies Reports of Huge Performance Dip Due to Patches for CPU Security Bug
- OS Makers Preparing Patches for Secret Intel CPU Security Bug
It is also strongly recommended that you read the security advisory by Google as it contains a very detailed description of these vulnerabilities.
If you are a vendor with a advisory or notice, please contact us to have your information added.
Last Updated: 01/05/18 16:52 EST
Official Advisories, Notices, Patches, or Updates:
Amazon
Amazon has released a security bulletin that provides information on how Amazon AWS services are affected by Meltdown and Spectre. In summary, this bulletin states:
This is a vulnerability that has existed for more than 20 years in modern processor architectures like Intel, AMD, and ARM across servers, desktops, and mobile devices. All but a small single-digit percentage of instances across the Amazon EC2 fleet are already protected. The remaining ones will be completed in the next several hours, with associated instance maintenance notifications.
While the updates AWS performs protect underlying infrastructure, in order to be fully protected against these issues, customers must also patch their instance operating systems. Updates for Amazon Linux have been made available, and instructions for updating existing instances are provided further below along with any other AWS-related guidance relevant to this bulletin.
You can read the full security bulletin here: https://aws.amazon.com/security/security-bulletins/AWS-2018-013/
AMD
AMD has not released an official advisory where they essentially say that their CPUs are not vulnerable to the speculative execution vulnerabilities. Below is the table from this press release:
| Google Project Zero (GPZ) Research Title | Details | |
| Variant One | Bounds Check Bypass | Resolved by software / OS updates to be made available by system vendors and manufacturers. Negligible performance impact expected. |
| Variant Two | Branch Target Injection | Differences in AMD architecture mean there is a near zero risk of exploitation of this variant. Vulnerability to Variant 2 has not been demonstrated on AMD processors to date. |
| Variant Three | Rogue Data Cache Load | Zero AMD vulnerability due to AMD architecture differences. |
The full advisory can be found here: https://www.amd.com/en/corporate/speculative-execution
As the security landscape continues to evolve, a collaborative effort of information sharing in the industry represents the strongest defe
Furthermroe, Tom Lendacky, a software engineer at AMD, had posted a email to the Linux Kernel Mailing List stating:
AMD processors are not subject to the types of attacks that the kernel page table isolation feature protects against. The AMD microarchitecture does not allow memory references, including speculative references, that access higher privileged data when running in a lesser privileged mode when that access would result in a page fault.
Disable page table isolation by default on AMD processors by not setting the X86_BUG_CPU_INSECURE feature, which controls whether X86_FEATURE_PTI is set.
You can read the full post here: https://lkml.org/lkml/2017/12/27/2
Windows internals expert, Alex Ionescu also had this to say:
Android
The Android team has updated their January 2018 bulletin with the following note:
CVE-2017-5715, CVE-2017-5753, and CVE-2017-5754, a set of vulnerabilities related to speculative execution in processors, have been publicly disclosed. Android is unaware of any successful reproduction of these vulnerabilities that would allow unauthorized information disclosure on any ARM-based Android device.
To provide additional protection, the update for CVE-2017-13218 included in this bulletin reduces access to high-precision timers, which helps limits side channel attacks (such as CVE-2017-5715, CVE-2017-5753, and CVE-2017-5754) of all known variants of ARM processors.
We encourage Android users to accept available security updates to their devices. See the Google security blog for more details.
The full bulletin can be found here: https://source.android.com/security/bulletin/2018-01-01
Antivirus Vendors
Microsoft will only distribute the emergency update to users if a particular registry key has been made by an installed antivirus vendor. Kevin Beaumont has created a spreadsheet that keeps tracks of antivirus vendors and whether they make this key: https://docs.google.com/spreadsheets/u/2/d/184wcDt9I9TUNFFbsAVLpzAtckQxYiuirADzf3cL42FQ/htmlview
Below are links to various antivirus vendors who have released advisories:
- Emsisoft: https://blog.emsisoft.com/2018/01/04/chip-vulnerabilities-and-emsisoft-what-you-need-to-know/
- eScan: https://blog.escanav.com/2018/01/meltdown-spectre-cpu-vulnerabilities/
- ESET: https://www.eset.com/us/about/newsroom/corporate-blog-list/corporate-blog/meltdown-spectre-how-to-protect-yourself-from-these-cpu-security-flaws/
- Sophos: https://community.sophos.com/kb/en-us/128053
- Trend Micro: https://success.trendmicro.com/solution/1119183
- Webroot: https://community.webroot.com/t5/Announcements/Microsoft-Patch-Release-Wednesday-January-3-2018/m-p/310146
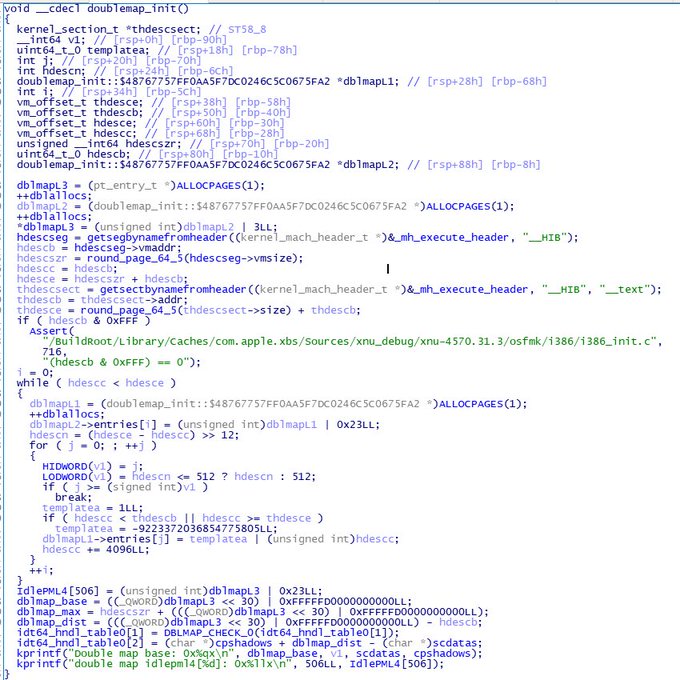
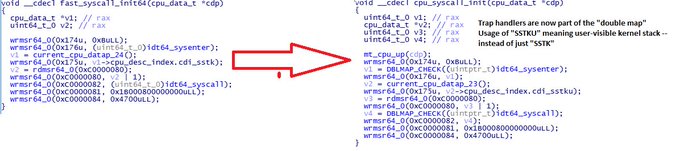
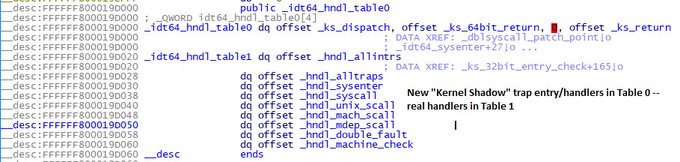
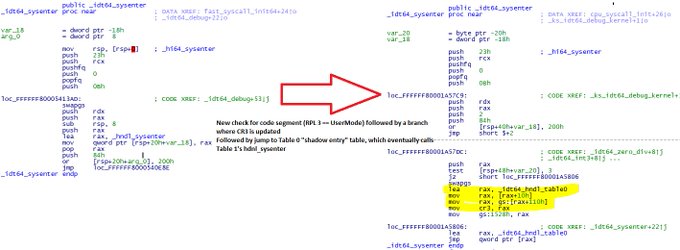
Apple
Apple has released an official advisory that states:
Security researchers have recently uncovered security issues known by two names, Meltdown and Spectre. These issues apply to all modern processors and affect nearly all computing devices and operating systems. All Mac systems and iOS devices are affected, but there are no known exploits impacting customers at this time. Since exploiting many of these issues requires a malicious app to be loaded on your Mac or iOS device, we recommend downloading software only from trusted sources such as the App Store. Apple has already released mitigations in iOS 11.2, macOS 10.13.2, and tvOS 11.2 to help defend against Meltdown. Apple Watch is not affected by either Meltdown or Spectre. In the coming days we plan to release mitigations in Safari to help defend against Spectre. We continue to develop and test further mitigations for these issues and will release them in upcoming updates of iOS, macOS, and tvOS.
The full advisor can be read here: https://support.apple.com/en-us/HT208394
Windows internals expert, Alex Ionescu had this to say:
ARM
ARM has released a security bulletin that lists the ARM processors that are susceptible to the Meltdown and Spectre attacks.
Based on the recent research findings from Google on the potential new cache timing side-channels exploiting processor speculation, here is the latest information on possible Arm processors impacted and their potential mitigations. We will post any new research findings here as needed.
The full ARM security bulletin can be found here: https://developer.arm.com/support/security-update
Chromium Project
The Chromium Project has issued an advisory where they provide best practices for web developers and recommend that Chromium users enable Site Isolation.
The full advisory is here: https://www.chromium.org/Home/chromium-security/ssca
Computer Emergency Response Team (CERT)
CERT has issued an advisory regarding thee Meltdown and Spectre CPU vulnerabilities. This advisory can be found here: https://www.kb.cert.org/vuls/id/584653
As Google was one of three teams that discovered this bug, they have some of the most detailed information regarding Spectre and Meltdown. A detailed bulletin regarding what Google products are affected by these vulnerabilities and how they are being mitigated can be found here: https://support.google.com/faqs/answer/7622138
I strongly suggest that everyone read the following articles for detailed technical information:
- https://meltdownattack.com/
- https://googleprojectzero.blogspot.co.at/2018/01/reading-privileged-memory-with-side.html
Google has also issued a bulletin for users of Google Cloud, G Suite, and Chrome. To summarize, this bulletin states that Google Cloud & G Suite have been updated to mitigate these vulnerabilities. If a customer uses their own operating system then they will need to install any related OS updates. Finally, Chrome & ChromeOS users can turn on Site Isolation to provide further protection.
The full bulletin can be found here: https://blog.google/topics/google-cloud/what-google-cloud-g-suite-and-chrome-customers-need-know-about-industry-wide-cpu-vulnerability/
Intel
Intel has released a press release regarding these vulnerabilities. A portion of this press release states:
Intel and other technology companies have been made aware of new security research describing software analysis methods that, when used for malicious purposes, have the potential to improperly gather sensitive data from computing devices that are operating as designed. Intel believes these exploits do not have the potential to corrupt, modify or delete data.
Recent reports that these exploits are caused by a “bug” or a “flaw” and are unique to Intel products are incorrect. Based on the analysis to date, many types of computing devices — with many different vendors’ processors and operating systems — are susceptible to these exploits.
The full press release can be found here: https://newsroom.intel.com/news/intel-responds-to-security-research-findings/
Linux Foundation
Thomas Gleixner, a Linux kernel developer, posted in December to the Linux Kernel Mailing List about new KAISER isolation patches. These are suspected to have been introduced to resolve the Meltdown and Spectre bugs in Linux. If anyone has more information, I would appreciate you letting me know.
The mailing list post can be found here: https://lkml.org/lkml/2017/12/4/709
Microsoft
Windows Information:
On January 3rd 2018, Microsoft released emergency out-of-band updates for Windows 7 SP1, Windows 8.1, Windows 10, and various Windows Server versions. Though these updates help to mitigate the Spectre and Meltdown speculative execution side-channel vulnerabilities, but to be fully protected you will also need to install the latest firmware & bios updates for your computer.
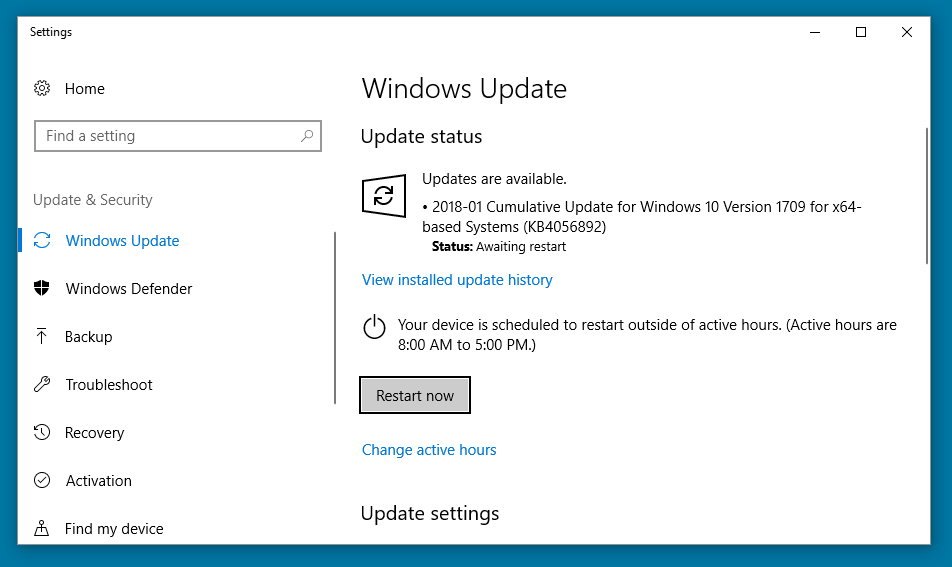
Advisories for these updates can be found here:
- Windows Server Guidance to protect against the speculative execution side-channel vulnerabilities
- Windows Client Guidance for IT Pros to protect against speculative execution side-channel vulnerabilities
Microsoft Edge Information:
Microsoft has released an advisory specifically related to Microsoft Edge. This advisory states:
Initially, we are removing support for SharedArrayBuffer from Microsoft Edge (originally introduced in the Windows 10 Fall Creators Update), and reducing the resolution of performance.now() in Microsoft Edge and Internet Explorer from 5 microseconds to 20 microseconds, with variable jitter of up to an additional 20 microseconds. These two changes substantially increase the difficulty of successfully inferring the content of the CPU cache from a browser process.
We will continue to evaluate the impact of the CPU vulnerabilities published today, and introduce additional mitigations accordingly in future servicing releases. We will re-evaluate SharedArrayBuffer for a future release once we are confident it cannot be used as part of a successful attack.
The full advisory can be found here: https://blogs.windows.com/msedgedev/2018/01/03/speculative-execution-mitigations-microsoft-edge-internet-explorer/
Azure Information:
Microsoft also released a compatibility note that you should read in order to understand why you may not see these updates being offered: https://support.microsoft.com/en-us/help/4072699/important-information-regarding-the-windows-security-updates-released
For Azure users, Microsoft has released an advisory that states:
The majority of Azure infrastructure has already been updated to address this vulnerability. Some aspects of Azure are still being updated and require a reboot of customer VMs for the security update to take effect. Many of you have received notification in recent weeks of a planned maintenance on Azure and have already rebooted your VMs to apply the fix, and no further action by you is required.
The full Azure advisory can be found here: https://azure.microsoft.com/en-us/blog/securing-azure-customers-from-cpu-vulnerability/
Mozilla
Mozilla has released an advisory stating that older versions of Firefox are susceptible to these attacks. To mitigate these attacks, starting in Firefox 57, Mozilla has reduced the precision of Firefox’s internal timer functions. Therefore, all Firefox users should upgrade to Firefox 57 for the extra protection.
The advisory can be found here: https://blog.mozilla.org/security/2018/01/03/mitigations-landing-new-class-timing-attack/
Nvidia
Nvidia has released an advisory that states they currently believe their GPUs are not affected by this bug, but will continue investigating:
NVIDIA’s core business is GPU computing. We believe our GPU hardware is immune to the reported security issue and are updating our GPU drivers to help mitigate the CPU security issue. As for our SoCs with ARM CPUs, we have analyzed them to determine which are affected and are preparing appropriate mitigations.
The full bulletin can be found here: https://forums.geforce.com/default/topic/1033210/nvidias-response-to-speculative-side-channels-cve-2017-5753-cve-2017-5715-and-cve-2017-5754/
Redhat
Redhat has released an advisory that provides a list of affected products and their status. This advisory states:
Red Hat customers running affected versions of the Red Hat products are strongly recommended to update them as soon as errata are available. Customers are urged to apply the appropriate updates immediately. All impacted products should apply fixes to mitigate CVE-2017-5753 (variant 1) and CVE-2017-5754 (variant 3). CVE-2017-5715 (variant 2) can be exploited both locally and through the virtualization guest boundary.
The full advisory can be found here: https://access.redhat.com/security/vulnerabilities/speculativeexecution?sc_cid=701f2000000tsLNAAY&
SUSE
SUSE has posted an advisory related to these attacks that states:
SUSE engineers have been collaborating with our partners and the Linux community on upstream Linux kernel patches. As a result of that collaboration, we are now able to release patches for most recent SUSE Linux Enterprise (SLE) versions. Additional patches for other SLE versions and environments will follow shortly.
The full advisory can be found here: https://www.suse.com/c/suse-addresses-meltdown-spectre-vulnerabilities/
Ubuntu
Ubuntu has released an advisory that states new kernels will be available on the original disclosure date of January 9th. The full advisory can be read here: https://insights.ubuntu.com/2018/01/04/ubuntu-updates-for-the-meltdown-spectre-vulnerabilities/
VMware
VMware has released an advisory that contains information about what products are affected and available patches. This advisory can be found here: https://www.vmware.com/us/security/advisories/VMSA-2018-0002.html
Xen
The Xen Project has released an highly detailed advisory regarding how the Spectre and Meltdown vulnerabilities affect Xen hypervisors:
Xen guests may be able to infer the contents of arbitrary host memory, including memory assigned to other guests.
An attacker’s choice of code to speculatively execute (and thus the ease of extracting useful information) goes up with the numbers. For SP1, or SP2 on systems where SMEP (supervisor mode execute protection) is enabled: an attacker is limited to windows of code after bound checks of user-supplied indexes. For SP2 without SMEP, or SP3, an attacker can write arbitrary code to speculatively execute.
The full post can be found here: https://xenbits.xen.org/xsa/advisory-254.html